Read About - Cybersecurity Risk Management vs. Compliance: What’s the Difference for Growing Organizations?
Read About - Cybersecurity Risk Management vs. Compliance: What’s the Difference for Growing Organizations?April 20, 2026
Many mid-market organizations assume that if they “pass the audit” or meet a framework requirement, they’re secure
Read More » Read About - Advisory Analytics: Turning Technology Risk Data Into Actionable Business Insights
Read About - Advisory Analytics: Turning Technology Risk Data Into Actionable Business InsightsMarch 26, 2026
Most organizations collect large volumes of cybersecurity and IT risk data, but few translate that data into meaningful executive decisions
Read More » Read About - Third-Party Risk Management: Why Your Vendors Are Your Biggest Cybersecurity Exposure
Read About - Third-Party Risk Management: Why Your Vendors Are Your Biggest Cybersecurity ExposureMarch 25, 2026
Most organizations don’t get breached because their internal firewall “failed.” They get breached because a trusted third party software provider, managed service firm, payroll processor, or cloud vendor, became the path of least resistance
Read More » Read About - Cybersecurity Compliance Advisory: A Practical Guide for Mid-Market Organizations
Read About - Cybersecurity Compliance Advisory: A Practical Guide for Mid-Market OrganizationsMarch 17, 2026
Many mid-market companies assume that passing an audit equals strong cybersecurity
Read More » Read About - As the Conduent Breach Expands, What to Review Now
Read About - As the Conduent Breach Expands, What to Review Now Read About - Spear Phishing Prevention: A Guide for Business Owners
Read About - Spear Phishing Prevention: A Guide for Business OwnersFebruary 24, 2026
Effective spear-phishing prevention requires a "defense-in-depth" strategy that combines Phishing-Resistant Multi-Factor Authentication (MFA), AI-driven behavioral email filtering, and a culture of "out-of-band" verification
Read More »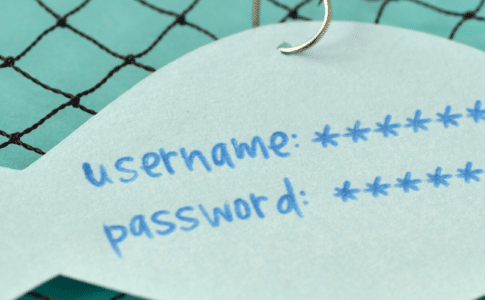 Read About - Phishing Emails: How to Recognize Them
Read About - Phishing Emails: How to Recognize ThemFebruary 17, 2026
A phishing email is a fraudulent communication designed to appear to come from a trusted source to steal sensitive business data, credentials, or funds
Read More » Read About - Cloud Security Threats and Challenges: A Guide to Protecting Client Data
Read About - Cloud Security Threats and Challenges: A Guide to Protecting Client DataFebruary 9, 2026
Cloud technology, including tools such as Microsoft 365 and AWS, offers essential flexibility but also introduces specific risks to your business and client data
Read More » Read About - Trustworthy AI Model Integrity: The Foundation of Responsible Automation
Read About - Trustworthy AI Model Integrity: The Foundation of Responsible AutomationFebruary 2, 2026
A trustworthy AI system consistently delivers reliable, ethical, and secure outcomes, offering a competitive advantage
Read More »